virus removal
Once again malware, Trojans, web browser redirections and unwanted pop ups are the flavour of the month. We have been removing a steady stream of Trojans and cryptoware from clients PCS. A somewhat common source seems to be gumtree. Many of our customers who have been infected use gumtree regularly and we all know they have had many issues in the past. While not pointing the finger at them directly it seems likely that these or other similar sites loaded with sidebar ads have been infected with malware.
If you see pops up your screen asking you to call a number for immediate removal, then contact us – DO NOT CALL the number!

Skype for Business Web Experience in Office 365
You can now launch and perform some basic Skype for Business tasks right from your navigation bar in Outlook on the web for business (Outlook Web App) in Office 365.
New features include:
- Launch Skype for Business from the navigation bar
- Search for people in your organization
- View your contacts list
- Start a conversation
- View your active conversations
- Leave a conversation

We can help you understand and use these new features, and take advantage of the benefits of accessing your office online wherever you are.
Get more detailed information about the new Skype for Business Web Experience.
Talk to us about the Office 365 Features you are not currently using and How you Can Benefit from Them
Moving from Evernote to OneNote
We use both Evernote and OneNote extensively and have a lot of experience with using both for individuals and teams.
If you are using Evernote then you may well have come across some of its limitations, including cost for premium product, no free form drawing, backups and other things where OneNote excels.
OneNote and Evernote are similar in many ways, but we think you’ll appreciate the advantages OneNote has to offer, including a free-form canvas where you can mix text, images, documents, handwriting, audio, video and more; free offline access; and unlimited monthly uploads.
Microsoft has now released an import tool to help you migrate. The OneNote Importer tool (for Windows initially) migrates all of your Evernote content into OneNote, giving you the opportunity to switch to OneNote and have all your notes in one place, on all your devices. They will deliver the Importer tool for Mac in the coming months.
More information and download the Evernote to OneNote importer.
If you want any more information on any of these features, how to use them or how they might affect you please contact us
Modern PCs
What is a modern PC? While not necessarily relating to form factors, there are plenty of new form factors around including 2-in-ones, tablets such as Surface and smaller tablet devices.
Let’s start with what is not a modern PC.
In the last 3-4 years a pc you bought would likely have been a tower PC desktop box, a thick and chunky laptop with not a lot of battery life – or you had to spend a lot of money to get a sexy thin one.
Now however we have available to us thin light tablets and laptops, incredibly long battery life and small form factor desktops.
A modern PC has these general characteristics:
- Thin, light and sexy designs
- Carbon, aluminium and shiny surfaces
- Massive screen resolutions – all the way up to 4K screens
- Touch screens, touchpads and keyboards with multiple functions and capability for swiping and gestures etc.
- Hardware capability security features like facial recognition, voice recognition and so on (biometrics).
- Great battery life. Full stop. A modern device should get 6 hours or more – no more playing 2/3rds of a DVD before your battery runs out on the plane!

Most of these things are built around the new Intel 5th and 6th generation chips along with UEFI hardware security features. These new chips support the great innovations being delivered by Microsoft through Windows 10 – now being delivered as soon as they are designed through the new operating system update features. These include the enhancements to battery life and performance that give us these amazing results.
So if you are not getting these things then you don’t have a modern PC.
BUT - BEWARE. Most of the PC retailers are not telling you these things. They are shifting units in volume, and they have lots of stock left of old PCS. They are shifting them out for cheap prices and many people are being sucked into buying them thinking they are getting a good deal. Many of these units currently on sale are effectively sporting hardware that is 2-3 years old inside. It is already one cycle out of date.
If you are getting near to an update or refresh of your hardware, or frustrated with the speed, battery life, low screen resolution of your current unit, then please talk to us first. We can easily and quickly let you know if the devices you are looking at are a good idea or not. Make sure you future proof your purchase to give you at least a 3 year life.
If you want any more information on how to identify whether the PC you are looking at is old or modern or just advice on what to buy please contact us
Note: We are also a Flexirent dealer and able to assist you to lease a new machine, or purchase it outright
Follow Us On Social Media
As always Jethro is your web, cloud and technology specialists. I am constantly learning new things and spending time researching, playing and testing new systems and reading about other people in the IT world doing the same thing. If you want to follow along with what I share in various spaces, then connect with me:
- Twitter https://twitter.com/spyjournal technology, cycling, social media, management, business, and web
- Linked In http://www.linkedin.com/in/jethromanagement
- Delicious https://delicious.com/jethrocon saved links
- Blog http://spyjournal.biz all sorts of stuff including personal and family updates
- Spyjournal Facebook https://www.facebook.com/spyjournal.biz tech, cycling, and other stuff
- Subscribe to our daily Newspaper https://paper.li/spyjournal/1345852972
- Subscribe to our weekly Newspaper https://paper.li/spyjournal/1345853288
- Jethro Management Facebook https://www.facebook.com/JethroManagement business, management, web
- Jethro Marketing Facebook https://www.facebook.com/JethroMarketing social media, marketing
- Dreamcoat Photography Facebook https://www.facebook.com/DreamcoatPhotography
- Dreamsport Photography Facebook https://www.facebook.com/DreamSportPhotography
- Red Hot Snapper Facebook https://www.facebook.com/redhotsnapper roller derby
Who is Your Trusted IT Advisor?

We act as a trusted advisor for many of our clients. What does that mean exactly?
Most business owners understand the importance of including their accountant and lawyer in any business changes that have legal or tax implications. It is very important to ensure that the right structures are in place to minimise tax, meet legal obligations and ensure that liability and risk are minimised and managed.
It is equally important to seek the advice of a trusted IT advisor in the same instances. An advisor sits on your side of the table, seeks to understand your business and can then make suggestions that are your in best interest. Here are some of the many reasons why this is important.
· Adding or terminating staff or employees should be done correctly. Ensuring they have the right hardware, software and access to corporate systems and data before they start work eliminates up front teething problems and gets them up to speed right away. Ensuring an employee’s access is removed BEFORE terminating reduces the risk of data theft and malicious behaviour.
- Technology can be configured many different ways, and what could be right for one scenario might not be right for another.
- Starting a new business, opening a new store, or even just working from home might require different security, backup solutions and data storage solutions. It is best to define these and understand the cost of implementation before the decision is made.
- Technology replacement plans should be in place to cycle hardware every few years. These may need to be modified if changes in ownership, downsizing or scaling up are planned.
So before you make important business decisions, contact us for a no obligation free chat. We would love to be your Trusted IT Advisor.
Kochie takes a Small Business through a Technology Makeover
David Koch from Channel 7 presented a small business makeover series with Microsoft last year. The 4 part series takes approximately 40 minutes to watch and is well worth the time taken.
If your business can relate to any of the problems presented here, or would like any of the solutions then please call us. This is what we do! Using technology correctly can improve workers productivity and business efficiency. Being able to do things for your customers your competitors can’t do may just give you the edge!
Talk to us about improving your Business Productivity and Efficiency with New Technology, Software, mobile access and better workflows
Windows 10 – Latest Version
Are you running the latest version of Windows 10 yet?
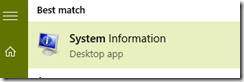
You can work it out by hitting the start button and typing System and clicking System Information.
In the OS Version you should see 10.0.10586 Build 10586. If not, you are running an older version.
You can update by running Windows updates and ensuring it downloads this new version.
Note: Check with us if you are not sure, or want support to running this version update.
And if you are running Windows 7 or 8 then time to upgrade – you have 3 months left for the free upgrade.
Book us in to upgrade your business or Home PCS to Windows 10 now - $150 per machine. conditions apply.
Security and Computing
Security is an ongoing battle of threats and defence. The cost to businesses to remove malware and viruses is a lot more than the small cost of educating yourself and taking appropriate defensive measures.
Are you up to date with the latest threats?
Three types of malware you should know about in 2016 Have you heard of the Brain Test, Zeus or Conficker threats? Are you safe? Read this article to learn more.
Who is most at risk of identity theft? You might be surprised to find out just who is more at risk of identity theft. Read this article to learn more. Or read our previous articles about protecting yourself and your business’s data.
Are you at risk from Spear Phishing attacks? Do you know how to recognise them and keep safe from them? There are many ways the attacks can come but the most popular delivery platform is email. As such, when opening an email it is important to know the hallmarks of a phishing scam:
- If it asks for your personal information, play it safe and assume it is a phishing attack.
- If you believe the email may be a scam, phone the organisation to verify if it is an official email.
- If you do click on a link, make sure to never enter your information into the website that appears.
- If you recognise the email address, do not take this as proof it is from an official or authentic source.
- If you see a suspect email has an attachment, make sure you do not open or download it as it could be an infectious computer virus.
Be safe and secure online – ask us how if you need to know more
Follow Us On Social Media
As always Jethro is your web, cloud and technology specialists. I am constantly learning new things and spending time researching, playing and testing new systems and reading about other people in the IT world doing the same thing. If you want to follow along with what I share in various spaces, then connect with me:
- Twitter https://twitter.com/spyjournal technology, cycling, social media, management, business, and web
- Linked In http://www.linkedin.com/in/jethromanagement
- Delicious https://delicious.com/jethrocon saved links
- Blog http://spyjournal.biz all sorts of stuff including personal and family updates
- Spyjournal Facebook https://www.facebook.com/spyjournal.biz tech, cycling, and other stuff
- Subscribe to our daily Newspaper https://paper.li/spyjournal/1345852972
- Subscribe to our weekly Newspaper https://paper.li/spyjournal/1345853288
- Jethro Management Facebook https://www.facebook.com/JethroManagement business, management, web
- Jethro Marketing Facebook https://www.facebook.com/JethroMarketing social media, marketing
- Dreamcoat Photography Facebook https://www.facebook.com/DreamcoatPhotography
- Dreamsport Photography Facebook https://www.facebook.com/DreamSportPhotography
- Red Hot Snapper Facebook https://www.facebook.com/redhotsnapper roller derby
Last week I promised to talk about viruses – but I ran out of time and space. I have included a section today for you. Hopefully you are protected against these serious threats to your business.
Also there are less than 2 weeks to our seminar with Richard Bowles. Please register your interest by return email so we can secure the right venue for the number of people coming. This will be a great day of working on your business and not just in it.
As always I am available to respond to your requests and queries and provide you with answers.
Viruses are a Serious Business Threat

Have you ever been hit by a computer virus? If you have you will know just how annoying they can be. Even the “non-malicious” ones can suck away time by popping up ads, redirecting your browser or just slowing your computer down.
In this short summary I will identify the main types, causes and protection against malware and viruses.
Virus Types
First of all this is more than just viruses as a technical definition. I have included all the potential threats that can be injected into your computer against your will (either by someone else or by yourself accidentally). I have also summarised them by the threat result not the signature or type as defined by the security experts.
Browser Redirect
This is where your browser settings are hijacked and when you type in a web address your browser sends you somewhere else. It may also include pop ups and potentially the sites that you are sent to won’t let you leave without clicking through a number of dialog boxes. Typically these come from an extension or add in that often was not deliberately installed.
Malware / Adware
These are usually “harmless” in that they don’t attack your system or data, but they do popup ads constantly when browsing. These are similar to the browser redirect but often they came in via some software that was deliberately installed and included unknown and unrequested additional software.
Data Attacks
These attacks are malicious in that they can overwrite data, lock data against use with ransom requests, or even delete data. Typically they are introduced via an attachment in an email.
System Attacks
I have grouped together here all the attack types that damage your system, including boot sector viruses, file infectors, directory viruses and so on.
How they come
The two main ways that viruses are injected into your computer are via an attachment in email or from an infected website.
In order to protect against either a complex layer of threat protection must exist. Stopping attacks before they can even be clicked on is the best form of defence.
Unfortunately many people use a mish-mash approach to threat protection. While an individual pc at home is reasonably isolated and an infection can be cut out fairly easily with usually minimal loss and cost, the same is not true in an office of connected PCs. One user who clicks on a payload that installs and then replicates over your network can have devastating effects on employee downtime, loss of data, cost to remove and rebuild machines, and subsequent protection.
Many businesses also play the “lets buy every protection we can get” game with multiple software based solutions including firewalls, internet protection software and antivirus software and so on. This is actually a false protection in many instances because these overlapping technologies create gaps and cracks, often caused by the users themselves “allowing” threats through.
In addition users are often the worst threat to a business by losing computers and mobile devices that are insecure, providing the recipients of the unlocked devices with legitimate access to the businesses data and IT systems, and in using insecure email applications to access mail.
Best Practice Protection for your Business
Microsoft are the leading computer and software provider in this space. The combined hardware and software layered approach to threat protection includes the following aspects:
Hardware
Bit locker is available to encrypt hard drives. A lost device is no longer something to worry about.
UEFI Secure boot. Windows 10 has introduced the ability to lock the boot process to secure OS only, reducing the chance that a corrupt OS (loaded with malware or viruses) can even execute.
Better passwords. Multi factor authentication is removing passwords altogether.
Mobile Device Management. Online management of all your mobile devices including remote wipe is possible with Office 365.
Software
In front of the business. Forefront security is provided in Exchange for all those using Office 365. Spam and Malware threats are removed before they can even come to an email user.
In the business. Outlook has a sandboxed approach to allowing access to attachments reducing the chance that an infected file can be even opened let alone do anything once it is opened by a user who ignores all the warnings.
Windows Defender provides real time attack management identifying and quarantining malicious files downloaded from the internet.
Internet Explorer contains a Smart Screen filter and other browsing enhancements designed to recognise and stop potential website injected threats from being accessed or deployed.
Afterwards
If you are attacked, then there are some things you can do. First remove the machine from your network immediately. Disconnect the network cable, or turn off the Wi-Fi. Better yet turn the machine off and deliver it to someone like us to clean.
Ensure you have a data recovery clause in your insurance policy. Check with your broker, these clauses normally cost nothing to insert and can cover you for at least $5ooo to restore data after an insurance claim for damage.
Summary
Businesses cannot legitimately ignore the real threats that malicious software can pose on their business.
A multi layered protection is necessary and that includes training users.
Using numerous different protection systems is usually worse not better.
Microsoft’s layered approach using Windows 10 modern devices, Office 365, Windows Defender and Internet Explorer provides the best possible defence system. Mac users are also protected by using Office 365 from spam and malware, but they are still open to website based attacks.
Contact us now if you need to determine if your business is secure against these threats. We can have an obligation free chat about your specific scenario and what you can do about it.
An Extremely Unique Opportunity By An Extreme Individual
 Learn the latest strategies in mastering your own mind, so you can fully commit & engage in the goals that you have set for yourself.
Learn the latest strategies in mastering your own mind, so you can fully commit & engage in the goals that you have set for yourself.
Richard Bowles holds world records on pretty much every continent on the planet, running the world’s longest and most rugged mountain ranges spanning from 1000km to 5,500km in length. Running up to 95km a day for weeks at a time, while tackling some of the most hostile weather and demanding terrain that the world has to offer, while carry all that he needs on his back.
Crocodile infested waters, exploding volcano’s, angry farmers with shot guns and being in the centre of a middle eastern desert warzone under missile fire is all in a day’s work for Richard, all the time pushing through the mental and physical barriers to conquer his success.
Over the last five years he has worked with some of Australia’s leaders in psychology and human performance, unpacking his own huge achievements to explore what it takes to succeed at any goal that is set before you, no matter the challenges and adversity that will be faced.
As a commitment and engagement strategist Richard helps you understand what is vitally needed to gain the goals that you have set for yourself. From his in-depth research he helps you understand that, Goals guide us, they don’t drive us.
If you are looking at a plan that will see you bullet proof your commitment to what you set out to achieve, and have you working towards your goals with ease, dedication and without burnout, then this is a seminar not to be missed.
We are partnering with Richard Bowles in delivering this exclusive seminar here in Brisbane CBD on the 3rd October from 9AM to 1PM. The cost is $89 and we will have a venue and ticketing options available soon.
Contact us today if you want more information.
New Gen6 CPUs and Motherboards now available
As mentioned in a previous newsletter the Computer Resellers often attempt to offload old stock at discount prices to susceptible buyers. The Core i3, Core i5 and Core i7 range of Intel chips are now in their 6th generation. The starting number of the chip name indicates the Generation. E.g. an Intel Core i5 6400 is a 6th Gen chip. If you are planning on buying a new computer there is no reason to purchase old technology as it will run slower, use more power and generate more heat. As the manufacturers improve the chips in each successive generation to use power more efficiently and produce more results so the capability of your machine improves. Saving $100 now can lead to hours of lost time “waiting” for your computer to catch up. It is also economically better to purchase a new machine now that will last for 4-5 years than an older machine that will last 2-3.
Talk to us today if you are in the market for new or replacement computers. We can sell all computer equipment and also provide financing if needed.
Free Business Digital Skills Webinars
Yes Free!
I will be running some digital skills webinars for free to any of our customers who would like to learn more about how to get the most out of their digital technology.
Each webinar will be aprox 20 minutes long and can be joined using a weblink. They will be run every 2-3 weeks on a Wednesday at 2pm. They will also be recorded and made available online.
Subjects will include:
· Mastering Email – tips and tricks for a zero inbox, reducing time spent in email and other shortcuts
· Basic Spreadsheet design
· Using OneDrive and SharePoint
· Understanding Social Media
· And more
Email me back on tim@jethromanagement.biz if you want to be added to the invite list. There is no obligation or cost to attend. You will need an invite link to join the webinar. I’ll add you to the list I already have and we will start once we have enough.
Social Media for Business
 Social media is constantly changing and it can be hard to keep up. There are always new features being added to the major social media sites like Facebook, LinkedIn, Twitter, Instagram, YouTube, and Pinterest. Managing even 2 or 3 of these accounts for your business can make your life busy. And even if you have the “luxury” of delegating it to a staff member it can cause anxiety hoping they are doing it right.
Social media is constantly changing and it can be hard to keep up. There are always new features being added to the major social media sites like Facebook, LinkedIn, Twitter, Instagram, YouTube, and Pinterest. Managing even 2 or 3 of these accounts for your business can make your life busy. And even if you have the “luxury” of delegating it to a staff member it can cause anxiety hoping they are doing it right.
Jethro has been active in managing social media accounts for many of our clients, from as little as creating the accounts and showing them how to use them to adding content and actively managing responses and engagement with customers. Just like you wouldn’t leave your phone ringing un-answered, so you should not leave comments and messages unanswered in Twitter, Facebook and LinkedIn.
We can establish networks relevant to your products and services, assist you to create and implement a social media strategy, run a one off campaign to improve engagement or around a specific event or just provide training for you or your staff in how to use these networks correctly for your situation.
If you want to talk more feel free to give me a call and discuss how we can help.
Follow us on Social Media
As always Jethro is your web, cloud and technology specialists. I am constantly learning new things and spending time researching, playing and testing new systems and reading about other people in the IT world doing the same thing. If you want to follow along with what I share in various spaces then connect with me:
- Twitter https://twitter.com/spyjournal technology, cycling, social media, management, business, and web
- Linked In http://www.linkedin.com/in/jethromanagement
- Delicious https://delicious.com/jethrocon saved links
- Blog http://spyjournal.biz/ all sorts of stuff including personal and family updates
- Spyjournal Facebook https://www.facebook.com/spyjournal.biz tech, cycling, and other stuff
- Subscribe to our daily Newspaper https://paper.li/spyjournal/1345852972
- Subscribe to our weekly Newspaper https://paper.li/spyjournal/1345853288
- Jethro Management Facebook https://www.facebook.com/JethroManagement business, management, web
- Jethro Marketing Facebook https://www.facebook.com/JethroMarketing social media, marketing
- Dreamcoat Photography Facebook https://www.facebook.com/DreamcoatPhotography
- Dreamsport Photography Facebook https://www.facebook.com/DreamSportPhotography
- Red Hot Snapper Facebook https://www.facebook.com/redhotsnapper roller derby
All content © Tim Miller. Feel free to share or send these emails on. If you want to unsubscribe just reply with Unsubscribe in the subject.